Hacker culture history: Since the 1983 release of the movieWarGames, the figure of the computer hacker has been inextricably linked to the cultural, social, and political history of the computer. That history, however, is fraught with complexity and contradictions that involve mainstream media representations and cultural anxieties about technology.
various hacker definitions
Hacker subculture
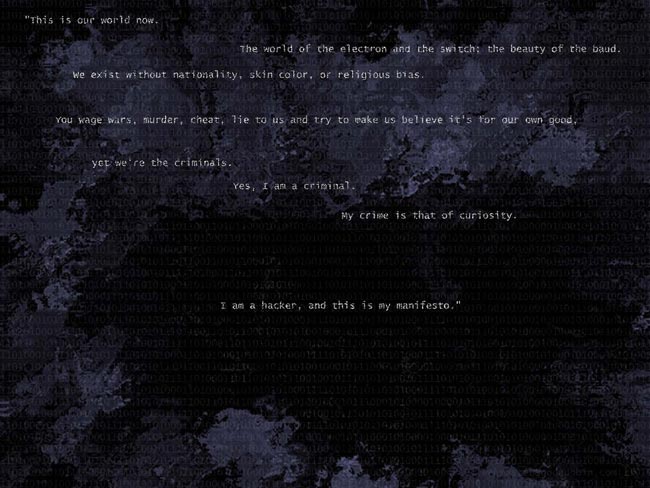
As a subculture, hackers have developed a particular sense of style that has been transformed over time and has been structured as an increasingly fluid and powerful form of resistance. As a youth culture, hackers are continually looking for ways to perturb or disrupt authority and challenge any understanding or representation of who they are. Hackers are not the only youth culture online. In fact, youth culture seems to have found the Internet to be the preferred medium for expression. Issues that have typically represented youth culture-rebellion, resistance, fan culture, music, fashion, and pop culture; all find expression in Social networks, Internet chat rooms, World Wide Web pages, e-mail mailing lists, forums and assorted other online elements. Hackers, however, illustrate a particular aspect of online culture that is more properly called a subculture, a culture that is both inherently tied to a larger, in this case, parental culture, but also resistant to it. The importance of online culture – particularly in the 1980s, 1990s, and up to the present – for youth culture is grounded in three factors. First, for the youth technology represents a way of doing things, a style, that is radically different from that of their parents. Second, Computer culture and computer style are in many ways the ideal hotbed for youth rebellion, as they require constant change in keeping with hardware and software developments. Third, the semiotic space that technology presents is one that is considerably less material than the traditional outlets of expression. Fashion, music, and literature, three primary outlets of youth culture expression, require a primary material component that is able to be marked, transformed, or reappropriated by mainstream culture. Computer culture, in contrast, is much less material in nature.
Origins of hacker culture
Hacker culture, born in the computer labs of East Coast universities in the late 1950s and 1960s, was a result of computer programmers doing everything in their power to beg, borrow, or steal computing resources. As a result, these hackers would often be forced to find time in the late hours of the night and into early morning, using less than ideal machines, and oftentimes being forced to work out clever compromises or work-around solutions to accomplish the task before them. The solutions, or “hacks,” permeated early computer culture, eventually becoming central to it. For example, hackers at major computer labs would engage in a process of “bumming” code. Each hacker would contribute to a program by finding increasingly elegant solutions to programming problems. In the mid-1970s, a computer whiz at Harvard dropped out, moved to New Mexico, and began writing software for the Altair 8800. His first program was a port of the computer language BASIC, made to run on the Altair. The computer whiz’s name was Bill Gates, and the company that he founded to write that software was Microsoft. The hobbyists who owned these new Altair computers had begun to find each other and form loosely knit groups. They also engaged in the process of “bumming code,” working to improve each other’s programs and programming skills by revising code. When these hackers got a hold of Altair BASIC, they set about distributing the code and working to improve it. Rather than paying the twenty five dollar fee to Microsoft, these hobbyists would make copies for their friends and give them away. The style that hackers adopted, particularly in places such as Homebrew, thus relied on an extensive knowledge of computer programming and, as was the case with the Altair, computer hardware and engineering as well. Premiums were put on experimentation and a style of “play,” which usually meant utilizing resources that were already at hand, rather than purchasing or adapting commercial applications. Hacker culture, as it would emerge in the underground of the 1980s and 1990s, would produce a new sense of style that would become divorced from the machinery that made it possible. In this process, hacker culture would undergo a stylistic transformation or mutation, making it both visible and highly resistant to incorporation.
2nd generation of hakers
Where WarGames spawned a generation of hackers in the mid 1980s, Hackers gave birth to a second generation of hackers in the 1990s. Hackers attracted the attention of a new generation of technologically literate hackers, who saw the Internet as the next frontier for exploration. The film spoke to this generation in the same way WarGames had spoken to earlier hackers, opening up a new world for exploration. Instead of focusing on the computer alone, Hackers introduced the new generation to the idea of a computer underground and the power of networked communication, things that older hackers had spent more than a decade building. Just as WarGames was the catalyst of the computer underground, Hackers sparked a second generation of hackers to follow the film’s mantras: “Hack the Planet” and “Hackers of the World Unite.” The messages of the two films, both deeply influential, were completely different and the subcultures that resulted from each would have very different perspectives. While the plot is pure Hollywood, the film’s attention to detail about hackers and hacker culture helped it gain the attention of some hackers in the underground. Of all the films about hackers, Hackers makes the most concerted effort to portray the hacker “scene” in some detail, even going so far as to get permission from Emmanuel Goldstein, the publisher of the hacker quarterly 2600, to use his name for one of the characters in the film. These hackers are not isolated loners or misunderstood teens; they are cutting-edge techno-fetishists who live in a culture of “eliteness” defined by one’s abilities to hack, phreak, and otherwise engage technological aspects of the world (including pirate TV and video games).
Hackers themselves have occasionally documented their own culture in an effort to resist media interpretations of their activities. One example of resistance is a film made by hackers themselves, showing the process of breaking into a telephone company control office and engaging in hacking practices. In it, two hackers, Minor Threat and Codec, enter the switching station of a telephone company and proceed to wreak havoc. During the course of their hacking exploits, they add free features to a friend’s phone, examine the desks of several phone company employees, fake a call from a telephone company official, and explore various areas of the building.
In the film Hackers, hacker style is manifested in the wardrobe of the hackers. While several characters dress in typical teenage garb, the two lead hackers (played by Johnny Lee Miller and Angelina Jolie) prefer a high-tech vinyl and leather techno-fetish look. Miller’s character (Dade Murphy, aka Zero Cool, aka Crash Override) and Jolie’s character (Kate Libby, aka Acid Burn) serve as representatives of the hacker-elite sense of style. Their look is urban-very slick and ultracool.
In contrast, hackers from Minor Threat’s film behave in a manner that betrays a more common theme in hacker culture, that of the outlaw. Reminiscent of Jesse James and the Old West, these hackers wear bandannas to cover their faces and conceal their identities. Rather than hiding their identities through high-tech wizardry, they, instead, carefully put on latex gloves before touching the computer console they hack to avoid leaving fingerprints. They have taken on the traits of criminals, burglars, or high-tech espionage agents.
Various members of hacker subculture
Computer security hackers
In computer security, a hacker is someone who focuses on security mechanisms of computer and network systems. subculture see their aim in correcting security problems and use the word in a positive sense. They operate under a code, which acknowledges that breaking into other people’s computers is bad, but that discovering and exploiting security mechanisms and breaking into computers is still an interesting activity that can be done ethically and legally.
Programmer subculture of hackers
In the context of computer security, a hacker is a person who follows a spirit of playful cleverness and loves programming. It is found in an originally academic movement unrelated to computer security and most visibly associated with free software and open source. It also has a hacker ethic, based on the idea that writing software and sharing the result on a voluntary basis is a good idea, and that information should be free, but that it’s not up to the hacker to make it free by breaking into private computer systems. The programmer subculture of hackers disassociates from the mass media’s pejorative use of the word ‘hacker’ referring to computer security, and usually prefer the term ‘cracker’ for that meaning. In the programmer subculture of hackers, a computer hacker is a person who enjoys designing software and building programs with a sense for aesthetics and playful cleverness.
Home computer hackers
In home computer context, a hacker is a computer hobbyist who pushes the limits of software or hardware. The home computer hacking subculture relates to the hobbyist home computing of the late 1970s, beginning with the availability of MITS Altair. An influential organization was the Homebrew Computer Club. However, its roots go back further to amateur radio enthusiasts. The hobbyists focus on commercial computer and video games, software cracking and exceptional computer programming (demo scene).
Subgroups in Hacker culture
White hat
A white hat hacker breaks security for non-malicious reasons, for instance testing their own security system. This classification also includes individuals who perform penetration tests and vulnerability assessments within a contractual agreement. This type of ‘white hat’ hacker is called an ethical hacker.
Black hat
A Black Hat Hacker is a hacker who violates computer security for little reason beyond maliciousness or for personal gain. Black Hat Hackers break into secure networks to destroy data or make the network unusable for those who are authorized to use the network.
Grey hat
A grey hat hacker is a combination of a Black Hat and a White Hat Hacker. A Grey Hat Hacker may surf the internet and hack into a computer system for the sole purpose of notifying the administrator that their system has been hacked, for example. Then they may offer to repair their system for a small fee.
Elite hacker
A social status among hackers, elite is used to describe the most skilled.
Script kiddie
A script kiddie is a non-expert who breaks into computer systems by using pre-packaged automated tools written by others, usually with little understanding of the underlying concept.
Neophyte
A neophyte, “n00b”, or “newbie” is someone who is new to hacking or phreaking and has almost no knowledge or experience of the workings of technology, and hacking.
Blue hat
A blue hat hacker is someone outside computer security consulting firms who is used to bug test a system prior to its launch, looking for exploits so they can be closed.
Hacktivist
A hacktivist is a hacker who utilizes technology to announce a social, ideological, religious, or political message. In general, most hacktivism involves website defacement or denial-of-service attacks. In more extreme cases, hacktivism is used as tool for cyber terrorism.